Applied cybersecurity training for OT or IT personnel
€4,610.00 excl. VAT
This training course is tailored for OT or IT personnel, junior cyber security engineers, junior SOC analysts and cyber security enthusiasts.
The training sessions will take place at the Thales Cyberlab in Tubize, Belgium (approx. 25 km / 35 min from Brussels).
Course dates
| 2023
Foundations (€ 2.865) : 16/10/2023 – 18/10/2023 |
If you are interested in the training course and you would like to be enrolled on a waiting list, or if you would like a dedicated session for your team (on-demand), please get in contact at laborelecacademy@engie.com |
Description
The global cyber threats continue to evolve at a rapid pace, with a rising number of data breaches each year. Medical services, big corporations and public entities experienced the most breaches, with malicious criminals responsible for most incidents. Some of these sectors are more appealing to cybercriminals because they collect financial and medical data, but not only all businesses that use networks can be targeted for customer data, corporate espionage, or customer attacks but also individual users can be targeting as well. At the same time, an increase in the cyber attacks within the Industrial Control Systems (ICS) has been observed. With the scale of the cyber threats to continue to rise, the need of cybersecurity awareness and cybersecurity solutions is vital.
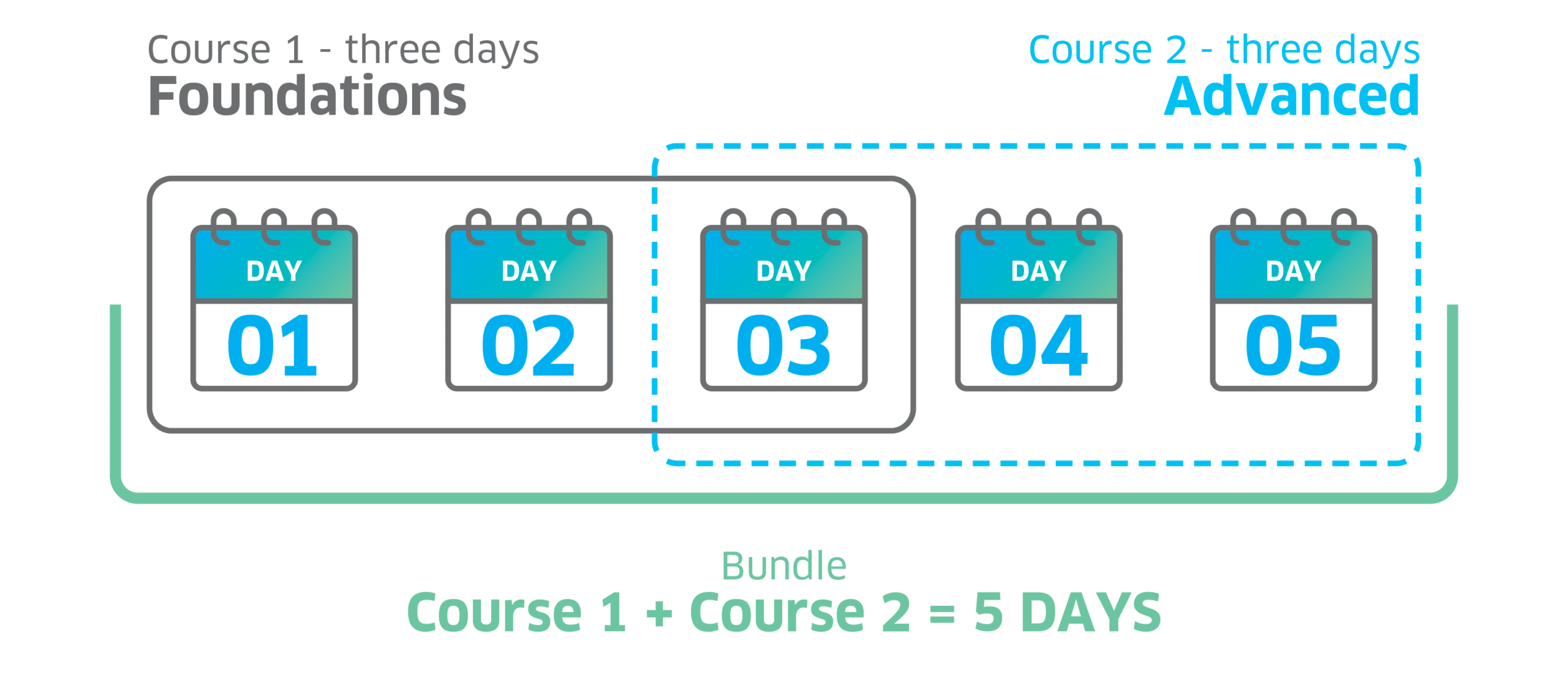
You can follow this training in two courses: Foundations and Advanced. If desired, you can also purchase this training as a bundle.
- The first part of the training (Foundations) focuses on introducing the technologies involved in modern control systems, and how they affect cybersecurity.
- The second part of the training (Advanced) focuses on covering the technical aspect of the first part by providing practical labs on building Pentest skills for accessing vulnerabilities and ways to attacks.
At the end of this training, the attendees will have both theoretical and technical knowledge on how to secure a network infrastructure as well as a Industrial Control System (ICS) environment from a technological point of view.
Course 1 – Foundations |
Course 2 – Advanced |
Duration3 days |
Duration3 days |
Price2865 € for a 3 days course, 4775 € for the 5-days bundle. Discounts will be offered for multiple participants from the same company. |
Price2865 € for a 3 days course, 4775 € for the 5-days bundle. Discounts will be offered for multiple participants from the same company. |
Course descriptionData breaches in Industrial Control Systems (ICS) are happening at an alarming rate. It’s no longer a question of whether a breach will happen, it’s really more a question of ‘are we ready for it?’. Within an organization there are operational technology systems and information technology systems. Both technologies and each set of systems were purpose-built, and neither was designed to work with the other. Therefore, this training course will help organization to build the bridge towards collaboration between IT and OT personnel to manage and maintain cybersafe culture. As the threat landscape from IT has merged into OT (Operation Technology) availability world due to its embedded IT concepts. Which requires to build enough technical capabilities to form a resilient workforce and implement new security policies and strategies. The purpose of this 3 days foundation course is to provide people with an understanding of the technologies involved in modern control systems, and how they affect cybersecurity. The goal is not to demonstrate hacking tools, or to explain to people how to use hacking tools but to give an introduction to the technologies that are used in the systems and explain to them how to secure those systems. At the end of this training, the attendees should have a good understanding on how to secure an ICS from a technological point of view. This training also focuses to build basic knowledge in Pen-testing skills for accessing vulnerabilities and ways to attacks. At the end of this training, user will have both theoretical and technical knowledge on Industrial protocols, OT infrastructure architecture, hardening and best practices for security solution deployment for securing control systems. Furthermore, user will also gain knowledge on the elements of IT networking model, tools to identify vulnerabilities and exercise to penetrate basic vulnerabilities. Also, this course will help users to fullfil the requirements for attending advance course (Course 2 – Advanced). |
Course descriptionThis training is essential to raise awareness by providing real-time demonstration of different cyber-attacks and to provide close-to-reality exercise related to cybersecurity of different fields including Operation Technology (OT) and Information Technology (IT) systems, individual users and corporate networks. The main goal of this training is to prepare the cybersecurity workforce of tomorrow and to keep current cybersecurity workers up-to-date on skills and current threats. During this training you will be able to experience a unique opportunity by visiting and having access to Thales Belgium’s CyberLab. CyberLab allows the replication of network topologies to act as realistic cyberbattle fields for subject-specific trainings, and also for close-to-reality exercises. Through this virtualized environment, scenarios of attacks/defenses are performed during immersive trainings on IT environments. During such events, the team in charge of defending the IT infrastructure will face various attacks using different vectors and means. Having realistic scenarios is thus a precious asset as this will help to train you in order to deal with recent attacks, executed as close to reality as possible. At the end of this training, you will have both theoretical and technical knowledge on how the Blue Team, Red Team and Purple Team exercises are performed within an industrial environment. Furthermore, you will able to get in contact with different types of cyberattacks before you actually face them in your own network and on the top of it you will get to know how you can secure a network infrastructure as well as an ICS environment from these kinds of attacks. |
PrerequisitesBasic knowledge of the Microsoft Windows operating environment. |
Prerequisites
|
Target audienceTechnical enthusiast personnel in ICS operations and maintenance departments, designated single point of accountability (SPoA), IT engineers and cybersecurity teams. |
Target audienceCybersecurity technical enthusiasts, IT engineers, IT teams, technical enthusiast personnel in Incident Management (ITSM), operations and maintenance department, designated Single Point of Accountability (SPoA). |
Mode75% theory – 25% practice. We will not be demonstrating hacking tools or how they are used. |
Mode10% theory – 90% practice |
Instructors |
Instructors |
Instructor

Soultana Ellinidou
Instructor

Prateek Arora
Additional information
| Select your Course type | Course 1 – Foundations, Course 2 – Advanced, Bundled Course |
|---|---|
| Select date | 2023 |
Instructor

Soultana Ellinidou
Soultana Ellinidou recently joined Thales Belgium as Cybersecurity Engineer. She holds a PhD degree in Engineering Sciences and Technology from Cybersecurity Research Center of Université Libre de Bruxelles (ULB). Furthermore, she was Teaching Assistant Instructor for the master class: “Communication Networks: Protocols and Architecture” during the past 4 years, organizing lab sessions and projects related to network security. She has 4 years experience in cybersecurity and network virtualization.

Prateek Arora
As senior consultant for ENGIE Laborelec, Prateek specializes in industrial automation and control system cybersecurity. He has more than eleven years of rich experience in handling projects related to governance, risk management, and compliance (GRC), architecting and implementing innovative technologies for a wide range of industries including oil & gas, and energy and water utilities, principally in the Middle East, Asia and Africa.
Frameworks
Goals
Program
//
Target Audience
//
Practical Info
//